Download and print the PDF or read the accessible version:
6. Contribute to information sharing with other services (as authorised by legislation)
6.1 Overview
The guidance in this chapter is intended to be general as each individual victim survivor’s level of risk, circumstances, wellbeing and needs will require a unique response and will build on the outcome of risk identification, assessment or management (undertaken, or planned).
In situations involving children experiencing family violence, professionals can use the Family Violence Information Sharing Scheme to request and share information in order to assess and manage family violence risk, as well as the Child Information Sharing Scheme for broader safety and wellbeing issues.
Key capabilities
Professionals required to have knowledge of Responsibility 6 should be able to:
- Proactively share information relevant to the assessment and management of family violence risk, including under the Family Violence Information Sharing Scheme, privacy law or other authorisation at law.
- Proactively share information relevant to broader safety and wellbeing issues for children using the Child Information Sharing Scheme.
- Respond to requests to share information from other services.
The outcome of risk identification (Responsibility 2), assessment (Responsibility 3 or 7) or management (Responsibility 4 or 8), will inform the kinds of secondary consultation, referral or information sharing you should undertake.
Guidance which refers to a perpetrator in this guide is relevant to situations where an adolescent is using family violence.
Remember
Professionals and services are authorised to share information to inform risk assessment or management practice under a range of laws, including the Family Violence Information Sharing Scheme, the Child Information Sharing Scheme, the Children, Youth and Families Act 2005 and relevant Australian privacy laws. The guidance in this chapter will focus primarily on using the Family Violence Information Sharing Scheme and the Child Information Sharing Scheme where family violence risk is present.
Organisations should assist professionals and services to understand and apply these Schemes and other authorisations to share information applicable to their service.
6.2 Purpose of information sharing
Effective information sharing is crucial in keeping victim survivors safe and holding perpetrators to account.
Information can also be shared to promote the broader wellbeing and safety of children, which may or may not relate to their experience of family violence.
The Family Violence and Child Information Sharing Schemes aim to create a significant cultural shift in information sharing practice. These schemes are also underpinned by the MARAM Framework, as well as relevant best interests and developmental frameworks. Professionals in prescribed organisations all have a role in information sharing to improve risk assessment and management practice.
Many organisations, especially those with ongoing service engagement with perpetrators or victim survivors, hold information relevant to assessing and managing family violence risk or to promote the safety or wellbeing of a child.
Effective information sharing between professionals supports risk assessment and management by bringing together information that would otherwise be unknown. This information can be used by relevant professionals to remove or reduce risk (as far as possible) or prevent escalation.
Risk is dynamic and can change over time. Professionals with responsibility for ongoing risk assessment should continue to share information to support updating of risk management and safety plans for the victim survivor, as well as intervention action planning for perpetrators of violence. This is particularly important for victim survivors who are not directly engaged with specialist family violence services in an ongoing way, but only at points of crisis or escalation.
Information sharing often means victim survivors don’t have to repeat their story with each new service they engage with. It also enables new services to build on existing information.
6.3 Information sharing in structured professional judgement
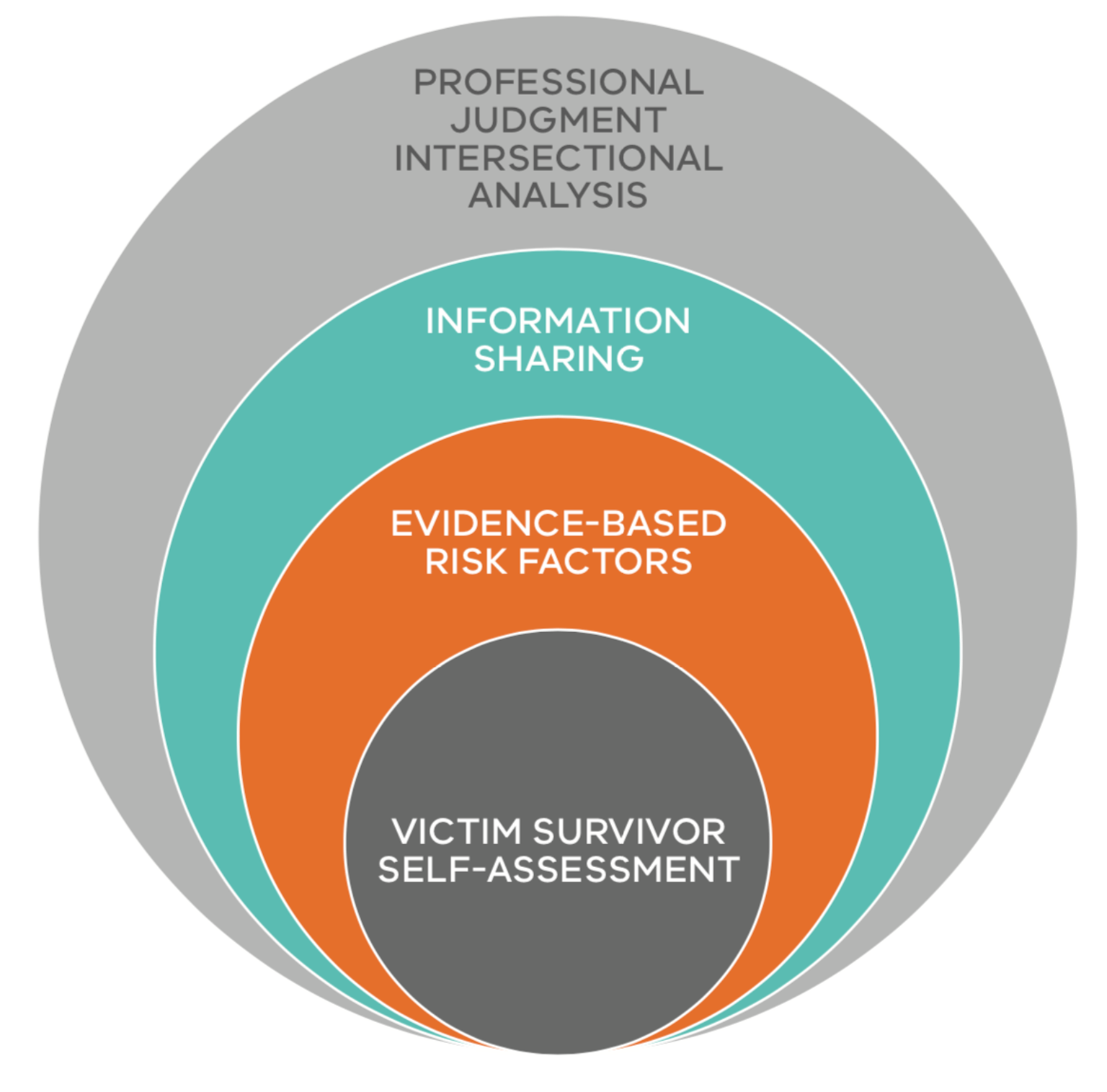
Information sharing is a key enabler of the model of Structured Professional Judgement as it supports professionals to share information to inform risk assessment. Information sharing may be authorised under a range of laws such as the Family Violence Information Sharing Scheme, the Child Information Sharing Scheme, the Children, Youth and Families Act 2005 or other relevant Australian privacy laws.
Sharing information assists professionals to identify additional risk factors or provide more information about known risk factors. This information can crucially inform the assessment of the level or seriousness of risk, and implementation of risk management responses as well as to promote the safety and wellbeing of children. Consider information sharing in each risk assessment you undertake, where services or engagement points are identified that may have information that would assist in the assessment or management process.
Key sources of information can be identified through consideration of protective factors or by using the genogram or ecomap exercises outlined in Responsibilities 7 and 8.
When assessing or managing risk to a victim survivor, consider how you might request and share information and ensure consent thresholds are met, where applicable. If consent for information sharing is not required, ensure that you take into account a victim survivor’s views if appropriate, safe and reasonable, particularly in relation to any past or recent experiences of service barriers or discrimination.
A victim survivor’s views expressed regarding information sharing should inform:
- Your approach to the information you request or share voluntarily.
- The professionals or services you are sharing information with voluntarily.
- How you might share information in response to a request.
Information sharing with other professionals and services should be used in conjunction with information gained from a victim survivor, including their self-assessment of risk, information about risk factors present and related circumstances, needs or wellbeing issues, that have been identified through risk assessment.
6.4 Reflecting on safe engagement, including for information sharing practice
Each victim survivor, both adults and children, should be considered individually for the services or supports they may need. This may be the first time a victim survivor has had their family violence risk, wellbeing or needs assessed, or they may have previously been connected to services. You should enquire about this to identify if there are any barriers to connection, or opportunities to reconnect to supportive services (see also Responsibility 4).
You should discuss options with victim survivors on the approach to referrals, and secondary consultation, including ongoing assessment and management. This will include your approach to prioritise and coordinate connection and referral to services. Prioritisation will be informed by your determination of the seriousness of risk, if you are responding to a crisis, and if connection to statutory service interventions are required. Responding to immediate risk is outlined in Responsibilities 2 and 4, and you may also use this guide to help you plan risk management responses and take action.
When seeking secondary consultation, making referrals or sharing information, you should be informed by an intersectional lens (See Foundation Knowledge Guide Section 9.4 and 9.5). In considering each service engagement, you should be guided by the individual’s identity and tailor your approach to referral, secondary consultation or information sharing accordingly. For example, if the victim survivor has let you know they are Aboriginal, identify as belonging to a diverse community, or are a child, young person or older person, consider if your service engagement would benefit from specialist advice or support.
Ask if the victim survivor would like to be directly connected to a service that specialises in working with individuals from their community group, or if they are comfortable with you sharing information with or connecting to that service for secondary consultation. The practice guide for Responsibility 1 will also assist with these aspects of practice.
Remember
Building and maintaining trust in the relationship with the victim survivor is essential to safe, ongoing engagement. It is particularly important to maintain trust and communication when connecting victim survivors to services and sharing information to promote their safety.
In most situations, referral does not mean you immediately cease your engagement with a victim survivor. Depending on your role, you will likely need to maintain engagement or continue to ‘check in’ with the victim survivor to support connection to a receiving service and respond to any issues that arise. This is also an important part of ongoing assessment and management of risk.
6.5 Legal authorisation to share relevant information
The Family Violence Information Sharing Scheme authorises organisations and services, prescribed through regulations, to share relevant information to assess and manage family violence risk.
Details of this scheme are outlined below and in the Ministerial Guidelines. Organisations may also have other permissions to share information to inform risk assessment and support coordinated and collaborative responses.
The Child Information Sharing (CIS) Scheme also allows organisations and services prescribed under that scheme to share information with each other to promote children’s wellbeing and safety1. This includes to promote the broader wellbeing and safety of children who experience family violence.
The CIS Scheme has been designed to complement the Family Violence Information Sharing Scheme. Refer to the guidelines for the CIS Scheme(opens in a new window) for further information.
Remember
If there is a serious threat to the life, health, safety or welfare of a person (such as serious risk of family violence), under the FVIS Scheme and privacy law you can share information, to lessen or prevent that threat without consent of any person. See the Office of Victorian Information Commissioner(opens in a new window) for further information.
As outlined in Responsibility 7, if serious risk has been identified through assessment via the MARAM Responsibilities for Practice Guide, this is considered to be an equivalent determination of ‘serious threat’ for the purposes of sharing information to lessen or prevent a serious threat under these Acts.
6.6 The family violence information sharing scheme
This section outlines key elements of the Family Violence Information Sharing Scheme (FVIS Scheme). Detailed guidance on the operation and use of the scheme are available in the Family Violence Information Sharing Guidelines.
Organisations and services that are prescribed under the FVIS Scheme are known as Information Sharing Entities (ISEs) and are authorised to share relevant information to assess and manage family violence risk2. The FVIS Scheme is intended to improve professionals’ and services’ ability to keep victim survivors safe and hold perpetrators in view and accountable for their actions and behaviours.
A subset of ISEs, known as Risk Assessment Entities (RAEs), have additional responsibilities to establish whether a risk of family violence is present, assess the level of risk posed and correctly identify the parties as the perpetrator or victim survivor through a comprehensive risk assessment.
A key component of the FVIS Scheme, is that information about an alleged perpetrator or perpetrator can be shared without their consent. Consent thresholds are further explained in Chapter 1 of the guidelines.
Some relevant sections of the guidelines are outlined below. However, you should refer to the guidelines for further information.
6.6.1 When can information be shared under the Family Violence Information Sharing Scheme?
There are two purposes for which ISEs can share information with each other under the FVIS Scheme:
- A family violence assessment purpose (to establish and assess risk):
The primary focus of a family violence assessment is on establishing whether a risk of family violence is present, assessing the level of risk the alleged perpetrator or perpetrator poses to the victim survivor, and correctly identifying the parties as the perpetrator or victim survivor.
- A family violence protection purpose (to manage the risk, including through ongoing risk assessment)
The family violence protection purpose means managing the risk of the perpetrator committing family violence, or the risk of the victim survivor being subjected to family violence. Information can be shared for this purpose when the presence of risk is known.
Managing risk involves removing, reducing or preventing the escalation of risk. As risk is dynamic and can change over time, information can be shared for ongoing risk assessment to monitor risk and escalation. For example, any ISE can request and share information from other ISEs to inform ongoing risk assessment and update risk management and safety plans with the victim survivor.
Remember
Any professional with a role in family violence risk assessment and management can undertake a risk assessment (in line with their role) under the MARAM Framework, such as screening, intermediate or comprehensive assessment. Information may be shared with all ISEs to undertake these functions to manage family violence risk.
Where it is not known whether family violence risk is present or the identity of a perpetrator is unknown or uncertain, then information may be shared with RAEs for an assessment purpose to establish risk or the identity of an alleged perpetrator.
If you have a reasonable belief that family violence risk is present and the identity of the perpetrator or victim survivor/s are clear (e.g. the victim survivor has identified the perpetrator), this would enable any ISE to share information under the FVIS Scheme for a protection purpose.
6.6.2 Talking about consent and information sharing with a victim survivor
In order to provide effective support to victim survivors it is crucial for you to build and maintain relationships of trust with them. An important way of achieving this is through open and transparent communication. This means making it clear that although you and your service will maintain confidentiality where possible, information sharing and other laws mean that relevant information may be shared without consent in some circumstances.
Chapter 9 of the Family Violence Information Sharing Scheme Guidelines provides information on the essential elements of consent, how consent can be given, how it should be documented and what to do when consent is refused or withdrawn.
Under the FVIS Scheme, various consent thresholds apply when information is being shared to assess or manage risk to adult and child victim survivors of family violence.
- Perpetrators and alleged perpetrators of family violence: Consent of an alleged perpetrator or perpetrator is not required when sharing their information under the FVIS Scheme (Chapter 3).
- Adult victim survivor: Consent is required to share information about an adult victim survivor (a person who is 18 years or over), unless the ISE reasonably believes that sharing confidential information is necessary to lessen or prevent a serious threat to an individual’s life, health, safety or welfare or the information relates to assessing or managing a risk to a child victim survivor (Chapter 4).
- Relevant third party: Consent is required to share information that identifies a relevant third party, unless the ISE reasonably believes that sharing confidential information is necessary to lessen or prevent a serious threat to an individual’s life, health, safety or welfare or the information relates to assessing or managing a risk to a child victim survivor (Chapter 4).
- Child victim survivors: Consent is not required from any person to share their information when you are assessing or managing risk for a child victim survivor (a child is someone who is under the age of 18 years, including infants and adolescents). However, where safe, appropriate and reasonable you should obtain the views of the child and/or other family members at risk of violence (including a parent who is not a perpetrator) prior to sharing their information (Chapter 5).
The Guidelines also provide information on having a conversation with an adult victim survivor about obtaining consent and limitations of consent (Appendix D) and a child victim survivor about their views and wishes (Appendix E) related to information sharing.
6.6.3 How can seeking consent or views inform your risk assessment or management planning?
Asking a victim survivor for their consent or views (as required) about what information is shared and the services you are sharing information with, can often assist you to understand more about the risk they are experiencing. This process can also highlight the barriers or discrimination a victim survivor may have experienced which may change the approach you take to secondary consultation or referral (see Foundation Knowledge Guide Section 9.4 and 9.5).
In situations where consent is not required (such as where there is a serious threat or if assessing risk to a child), you must seek the person’s views on what information is shared and the organisations or professionals you propose to share information with (noting that you are not required to seek consent or views from an alleged perpetrator or perpetrator to share their information).
A victim survivor’s views about information sharing can:
- Assist you to identify additional risk factors.
- Enable you to share information which would support culturally safe service from the receiving professional or service.
- Help you share information safely and mitigate future risk of unsafe information sharing by recording in safety plans any known issues with sharing to specific professionals or services.
Examples of where it may not be appropriate, safe or reasonable to seek views of a victim survivor are outlined in the Family Violence Information Sharing Scheme Guidelines(opens in a new window).
6.6.4 Information sharing under other laws
If you were already permitted to share certain information under existing privacy laws or another law before the Family Violence and Child Information Sharing Schemes commenced, you can continue to do so. The intersection of the FVIS Scheme and other laws is outlined in Chapter 11 of the Family Violence Information Sharing Guidelines.
6.7 Risk-relevant information
Understanding what information is ‘risk- relevant’ is central to family violence risk assessment and management practice. Also, information that is relevant for a family violence assessment or protection purpose can be shared under the FVIS Scheme.
Identifying what information is ‘relevant’ will:
- Be determined on a case-by-case basis for each victim survivor or perpetrator, depending on the family violence behaviours (risk factors) a perpetrator is using against a victim survivor, or each of their circumstances, or related wellbeing and needs to promote stabilisation and recovery.
- Be information that supports your assessment of current or future risk, which can include a perpetrator’s past behaviour. Information about a victim survivor’s past behaviour is less likely to be relevant.
- Depend on the purpose for which you are sharing the information, such as an assessment or protection purpose (see Section 6.6.1 of this guide and the Family Violence Information Sharing Scheme Guidelines for further information).
- Depend on your role and the role of the professional/service you are seeking information from or sharing information with.
- Depend on what action you want to take:
- Why are you seeking the information — how will this inform your family violence risk assessment or management role? (e.g. assessment or safety planning).
- What action do you want the receiving professional/service to take from your sharing the information?
Risk-relevant information may be information about a perpetrator (their behaviour or circumstances) or a victim survivor (the risk they are experiencing and their circumstances) or another person.
The information should be relevant to your decision-making for assessing or managing family violence risk, including stabilisation and recovery.
Information about perpetrator behaviour such as violence used against an adult or child, the presence of risk factors, or a perpetrator’s circumstances, are an important first point of reference for understanding what information is risk- relevant. Information that relates to any of the family violence risk factors is described in detail in the Foundation Knowledge Guide, and within the guidance on risk assessment in Responsibilities 3 and 7.
Relevant information may also relate to a victim survivor or perpetrator’s circumstances impacting risk management planning. These may include:
- Housing or employment of perpetrator (what is their location and whereabouts?).
- Health, mental health, or other wellbeing issues which influence behaviour, decisions or choices.
- Are there family law orders or intervention orders in place (e.g. exclusion conditions on intervention orders).
Some of these relevant circumstances may be identified through the risk assessment discussion with a victim survivor, or through consideration of the protective factors and safety planning. Further guidance on identifying relevant information about a perpetrator’s circumstances is outlined in Responsibility 7.
Risk management is defined broadly to include stabilisation and recovery, such as the impact of family violence on wellbeing and needs. Under the FVIS Scheme, this means risk-relevant information for a victim survivor, which includes information that relates to wellbeing and needs due to their experience of family violence.
Information relevant to promoting a child’s wellbeing or safety can also be shared under the CIS Scheme, including outside of the context of family violence. Information can be shared under the CIS Scheme if an ISE reasonably believes that sharing the information may assist another ISE to:
- Make a decision, an assessment or a plan relating to a child.
- Initiate or conduct an investigation relating to a child.
- Provide a service relating to a child.
- Manage any risk to a child.
Information may be sourced from:
- Disclosure and/or risk assessment with a victim survivor.
- Discussion from related third parties such as friends or family members.
- Victoria Police family violence incident information (your service may receive L17 referrals).
- Court records (that are not excluded).
- Other records from professional or therapeutic service and relevant databases.
The range of sources of direct disclosure will vary depending on your professional role. Other information can be requested through the schemes from other ISEs under the appropriate assessment or protection purpose, or other applicable authorisations.
If you are uncertain about what information is relevant to share, seek secondary consultation internally (within your organisation or service), or externally with a specialist family violence service. If you are concerned or unsure whether information is relevant, you can share information with a specialist family violence service through secondary consultation in a de-identified way.
Remember
You should be discerning about the information you are sharing. It is usually not appropriate to share ‘whole records’ without review of the content and scope of information contained within them, and you should be guided by the criterion above on the specific information that should be shared.
If working with the victim survivor you should seek their consent to share information, unless consent is not required, in which case you should seek their views, where appropriate, safe and reasonable to do so.
6.7.1 Sharing information relating to family violence risk for children and young people
Children should have their risk and related wellbeing and safety needs individually assessed as per guidance in Responsibility 3. Under the FVIS Scheme, information about any person that is relevant to assessing or managing family violence risk for a child can be shared by an ISE without the consent of that person.
However, where it is appropriate, safe and reasonable, you should seek the views of the child or young person, and a parent/carer who is not a perpetrator, on how their information is shared. These views should be taken into account when deciding what information should be shared, including what services you should voluntarily share this information with or how information might be shared when you are obliged to share. Where you have safety concerns about how, when and with whom information is shared, including where doing so may increase risk, this should be reflected in risk management and safety plans (see Responsibility 4).
You should make clear to parent/carers (generally mothers) that are not perpetrators, that if their information is shared despite their views, it is being shared to assess or manage risk to a child.
6.7.2 Method of information sharing
The FVIS and CIS Schemes do not dictate that information has to be shared in a specific way. It is common for information to be shared with another professional by a range of methods, including verbally (face-to-face), email and phone. This may depend on the policies of your organisation or the urgency of the request or sharing, and will often depend on whether there is an existing professional relationship or this is the first time you have made contact with a service or professional.
When the information sharing request is time critical, you can phone a professional or service in the first instance. You could then then choose to follow up by making the request or sharing the information in writing to enable you to document the request or sharing of information as part of your organisation's good record keeping processes. When sharing and storing information, organisations should follow their obligations for data security under privacy law, if applicable.
You should refer to your organisational policies on information sharing methods to guide you, including your authorisation to share under applicable information sharing laws and how to keep records of any information shared.
If you are uncertain, prior to sharing information, confirm by following your internal processes, such as consulting with a senior practitioner or team leader, or by secondary consultation, to determine if the information you are sharing is relevant to the purpose (for an assessment or protection purpose for the FVIS Scheme, or to promote the wellbeing of a child under the CIS Scheme). This will assist in the request process if the responding ISE raises questions about the relevance of information requested.
6.7.3 Collecting and recording information sharing
You should refer to your organisation or service’s policies and procedures on record keeping in relation to information sharing. The Family Violence and Child Information Sharing Schemes have specific record keeping requirements that are aligned.
The Family Violence Information Sharing Scheme Guidelines(opens in a new window) provide advice on what is required in Chapter 10.
The Child Information Sharing Scheme Guidelines also include information on record keeping and information management in Chapter 5.
As specified in the Ministerial Guidelines, ISEs should take reasonable steps to correct information recorded or shared about any person if an ISE becomes aware that the information is incorrect. This applies if the information is about a victim, perpetrator or third party.
Professionals should refer to their organisation’s policies and procedures to assist with correcting information. Inaccurate information should be corrected as soon as possible after you become aware the information is inaccurate and you should give prominence to any correction on the client’s file. This is particularly important if the information may put a victim survivor at risk or a victim survivor has been or may be misidentified as a perpetrator.
6.8 What's next?
Information sharing can continue to inform your actions for risk assessment and practice, depending on your role, under Responsibilities 3–4, or 7–8.
In some situations, it may be necessary to convene a coordinated response to family violence risk, or safety and wellbeing for children. If this is the case, refer to Responsibility 9 for further information.
Ongoing risk assessment and management is also a part of practice. You should regularly review the appropriateness of referrals and follow up with services on the success of the referral and how you can continue sharing information to inform your risk assessment or management approaches. For more information about ongoing risk management practice, refer to Responsibility 10.
6.8.1 Document in your organisation’s record management system
In addition to Section 5.6, it is important to document the following information in your service or organisation’s record management system:
- Copy of any risk assessment or safety plan you share with other services.
- Under what permission you requested or shared information e.g. Family Violence Information Sharing Scheme, Mandatory Reporting, other privacy law.
- What organisation or service was contacted for secondary consultation and who you spoke with.
- Method of request (email, fax, telephone).
- What information was requested, the date of request.
- If and what information was shared, the date, who the information was shared to.
- If a referral was made — to who and the purpose.
- Views of the victim survivor around secondary consultation.
- Outcomes of secondary consultation and referral.
1. Part 6A, Child Wellbeing and Safety Act 2005.
2. Part 5A of the Family Violence Protection Act 2008 (the Act). This information sharing scheme was introduced pursuant to recommendation 5 of the Royal Commission into Family Violence, which acknowledged that organisations that work with victims and perpetrators of family violence collect a wide variety of information in order to keep victims safe and hold perpetrators to account. The Commission also identified barriers that prevent information from being shared as effectively as it could be and found that the failure to share crucial information with frontline workers can have catastrophic consequences.
Updated